The 2016 Dyn Attack and its Lessons for IoT Security
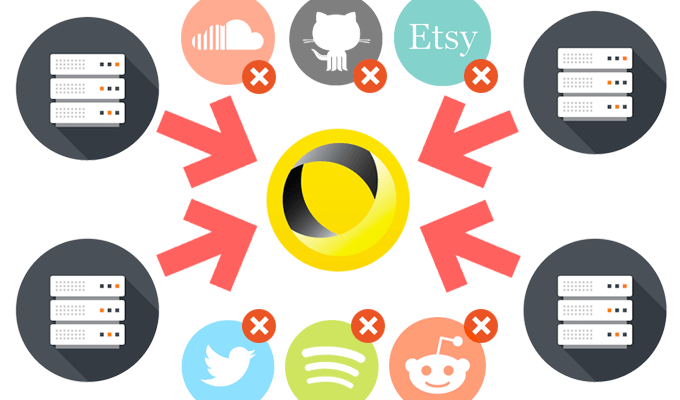
On October 21, 2016, the largest distributed denial of service (DDoS) attack took place, shutting down most of the Internet, including Twitter, Amazon, GitHub, and the New York Times.[1] The attack targeted Dyn, a company that services a large share of the internet’s domain name system (DNS) infrastructure, and lasted for most of the day. The type of malware used for the attack, which leveraged IoT devices rather than computers, resulted in an extraordinarily malicious attack, “roughly twice as powerful as any similar attack on record.”[2]
What made the Dyn attack unique was that the perpetrators used a specific type of “botnet” malware, which infects a network of computers and coordinates them to bombard specific servers with web traffic until the servers collapse. The Dyn attack used a “Mirai botnet,” which used internet of things (IoT) devices instead of computers. Employing this strategy gave the hackers many more devices to choose from (between 50,000 and 100,000), including home routers and video recorders.[3]
The perpetrators were able to access these IoT devices by hacking into them. Most of the IoT devices used for the Mirai botnet were running on default credentials. In fact, after the attack, the Mirai source code was posted online and included default credentials for more than 60 devices.[4]
The attack taught the world several valuable IoT security lessons:[5]
- Devices should always be able to have their software, passwords, and firmware updated. If these features cannot be updated, these devices should not be implemented as they are too vulnerable to attacks.
- Users should not be allowed to keep default credentials.
- IoT devices should require unique passwords per device.
- IoT devices should always be patched with up-to-date software and firmware.
Along with security lessons, the Dyn attack also showed the need for increased consumer vigilance regarding IoT devices. The devices presented a new point of vulnerability for both consumers and the Internet in general, and the attack taught a valuable lesson that with new technology and convenience also comes the need for increased awareness.
[1] https://www.networkworld.com/article/3134057/security/how-the-dyn-ddos-attack-unfolded.html
[2] https://www.theguardian.com/technology/2016/oct/26/ddos-attack-dyn-mirai-botnet
[3] https://www.networkworld.com/article/3134057/security/how-the-dyn-ddos-attack-unfolded.html
[4] https://www.forbes.com/sites/davelewis/2017/10/23/the-ddos-attack-against-dyn-one-year-later/#47df91f41ae9
[5] https://www.iotforall.com/5-worst-iot-hacking-vulnerabilities/
3 comments on “The 2016 Dyn Attack and its Lessons for IoT Security”
Comments are closed.


Claire,
I had done some research on this previously and greatly appreciate your post. I wanted to get your take on the responsibility that the companies must start to take. I do agree there are certainly things that the consumers must begin to do in order to ensure their systems are secure, but it seems oddly more one sided in the realm of cyber security than other places. For instances, its not typically the consumers job to verify the security of their vehicles they buy, yet it does fall to them to change their default passwords. I wonder if there is more companies can begin to do to share some of the security burden.
Any ideas?
Best,
Zac
Hi Zac,
That’s a great point that with technology, it seems the responsibility of cyber security falls more heavily on consumers. I think hardware IoT devices (I’m thinking of things like Nest, Alexa, etc.) could take on some of the burden by adopting the practices of fintech and credit card companies — specifically, monitoring the data they have access to for anomalies or for potential breaches. I think to ensure customers do their part, like resetting the default credentials and installing the proper software/firmware updates, companies will need to be more strict and maybe deny access until these are completed.
Agree with the lessons learnt to enhance the security of IoT devices. However, to enhance the security of the entire IoT ecosystem we need to enable solutions that prevent relying on the constant integrity of every single IoT device as no security is foolproof. There ought to be smarter self-correcting IoT systems that identify ‘malicious’ activity and suspend the culprit devices.